Livrare
Consilier de cumpărături





Nu se pretează? Nu contează! La noi puteți returna bunurile în 30 de zile
 Voucher cadou
orice valoare
Voucher cadou
orice valoare
Cu un voucher cadou nu veți da greș. În schimbul voucherului, destinatarul își poate alege orice din oferta noastră.
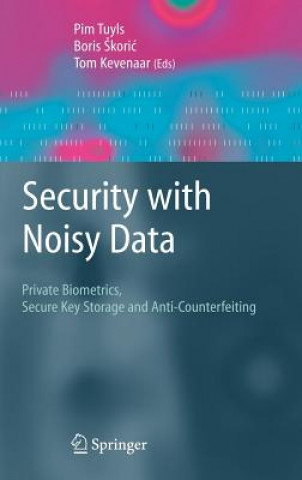
Security with Noisy Data
On Private Biometrics, Secure Key Storage and Anti-Counterfeiting
 engleză
engleză
 277 b
277 b
30 de zile pentru retur bunuri
Clienții au cumpărat de asemenea


Noisy data appear very naturally in applications where the authentication is based on physical identifiers. This book provides a self-contained overview of the techniques and applications of security based on noisy data.§It covers both the theory of authentication based on noisy data and shows it in practice as a key tool for prevention of counterfeiting. Biometrics and physical unclonable functions are discussed extensively. Key new technologies discussed include: -Algorithms to derive secure keys form noisy data in particular from Physical Unclonable Functions and Biometrics, - also the theory which proves that those algorithms are secure is made accessible; Practical Implementations of the above mentioned algorithms; - Techniques that give insight in the security of those systems in practice; An overview and detailed description of new applications that become possible by using these new algorithms.§This book can serve as a starting point for PhD students entering the field and will also benefit professionals.

Informații despre carte
 engleză
engleză

Dăruiește această carte chiar astăzi
Este foarte ușor
1 Adaugă cartea în coș și selectează Livrează ca un cadou 2 Îți vom trimite un voucher în schimb 3 Cartea va ajunge direct la adresa destinataruluiAr putea de asemenea, să te intereseze
Bună ziua! Sunt Libroamiko, consilierul dumneavoastră de cărți.
Cu ce vă pot ajuta?
 Contact
Contact Cum să cumpăr
Cum să cumpăr